Security
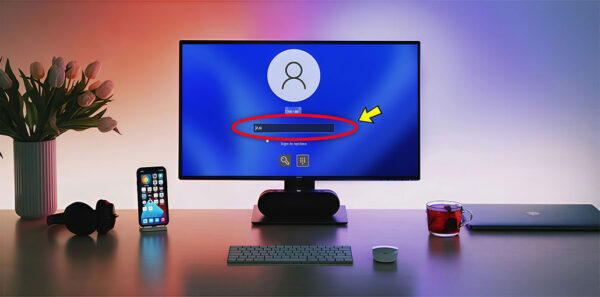
Something Happened and Your PIN Isn’t Available? 6 Easy Ways to Fix It
Why does it say something happened and your PIN isn’t available? What do you do if something happens, and your PIN isn’t available...
ByBarrett SMay 30, 2026How to Bypass Activation Lock on iPhone/iPad: 4 Simple Solutions
Activation Lock is an excellent way to keep your devices safe, but it can be a hassle when you need to bypass it...
ByAiden NathanMay 29, 2026Frontier AI Security: From Prediction to Trustworthy Intelligence | Act I — The Reality Check
Blog 1: Beyond the Metrics: Why Current AI Security Is No Longer Enough Artificial Intelligence (AI) has rapidly become one of the defining...
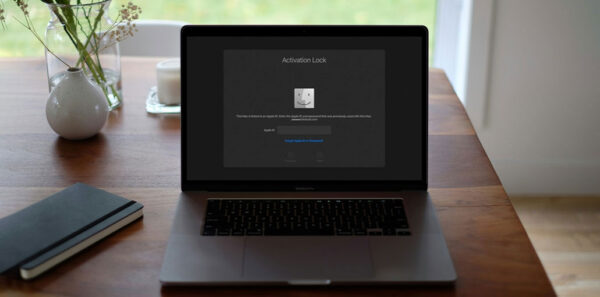
ByArash Habibi LashkariMay 28, 2026How to Unlock an iCloud Locked MacBook Pro: 3 Best Methods to Try
The iCloud activation lock is available across the Apple ecosystem. This safeguards against misuse of the MacBook Air, MacBook Pro, iPhone, iPad, and...
ByBarrett SMay 25, 2026How to Hide Messages on iPhone: Best Easy Methods for 2026
The Internet has become the primary driver for humanity and the world at large; it is becoming more challenging for people to keep...
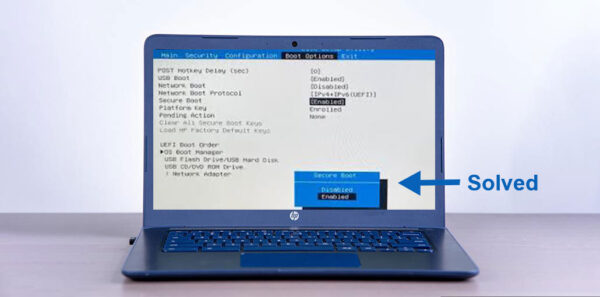
ByIsla GenesisMay 24, 2026How to Fix Secure Boot Enabled But Not Active in Windows 11
Secure Boot is a feature introduced by Microsoft in Windows 8 to ensure users’ security. This feature ensures that the OS on the...
ByAiden NathanMay 21, 2026From AI Foundations to AI Frontiers in Cybersecurity: The Journey of Behaviour-Centric Cybersecurity Center (BCCC) in Canada
Introduction Artificial Intelligence (AI) has rapidly transformed modern cybersecurity, enabling intelligent threat detection, malware analysis, behavioral monitoring, and automated defense mechanisms across complex...
ByArash Habibi LashkariMay 19, 2026Your IP Has Been Temporarily Blocked: Step-by-Step Fix Guide (2026)
If you’ve encountered the message “your IP has been temporarily blocked”, you’re likely to be confused and perhaps frustrated. But knowing what this...
ByZoey RileyMay 15, 20266 Easy Tricks to Remove Password from Excel in 2026
Excel is a well-known and popular software application that is used by a variety of businesses to create spreadsheets and collate data. It...
ByBarrett SMay 1, 2026Enter Password to Unlock 30/30 Attempts Remaining: Easy Fix Guide
Have you ever witnessed that “Enter password to unlock (30/30 attempts remaining)” message on your Android phone? If you activate the security feature...
ByBarrett SApril 22, 2026