In today’s world, every company, big or small, has valuable information online. Hackers are constantly looking for ways to steal it, and the consequences can be devastating. Breaches are expensive, both financially and in terms of lost trust. Cybersecurity experts help prevent them, saving you from hefty fines, legal battles, and reputational damage. In this article, let’s explore the significant benefits that businesses can get by investing in cybersecurity hiring.
Proactive Threat Mitigation
There’s no doubt that cybersecurity experts possess the skills and knowledge to identify potential vulnerabilities and weaknesses in a business’s digital infrastructure before they can be exploited by malicious actors.
By staying ahead of emerging threats, cybersecurity professionals implement preventive measures, reducing the likelihood of security breaches and ensuring a proactive defense posture for your business.
Rapid Incident Response
In the unfortunate event of a cybersecurity incident, the speed of response is crucial. Cybersecurity experts are trained to respond swiftly and effectively to security breaches, minimizing the impact on the business.
Their expertise in incident response includes isolating affected systems, conducting forensic analyses, and implementing recovery strategies. Rapid incident response is essential for mitigating damages, maintaining business continuity, and protecting sensitive data.
Expertise in Emerging Threats
The cybersecurity landscape is dynamic, with new threats constantly emerging. Cybersecurity experts are dedicated to staying up-to-date on the latest threats, attack vectors, and hacking techniques. Their expertise in understanding and countering emerging threats ensures that businesses are well-prepared to face the challenges posed by evolving cyber-attacks.
Continuous Security Monitoring
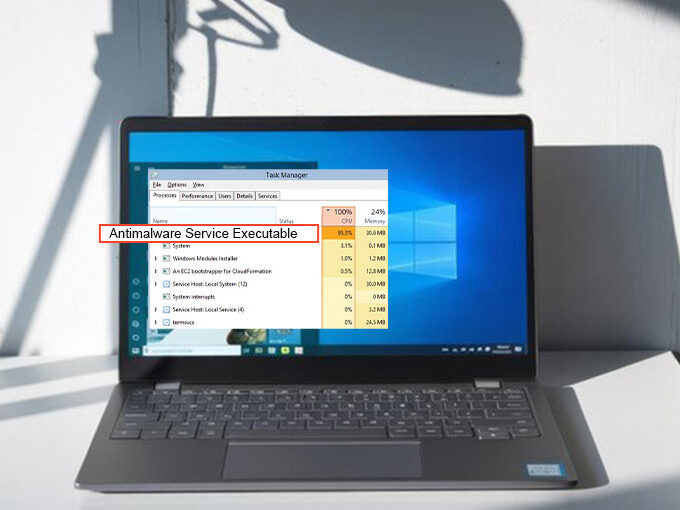
Effective cybersecurity is not a one-time effort but an ongoing process. Cybersecurity experts implement continuous security monitoring to detect and respond to threats in real time.
Through advanced monitoring tools and techniques, they identify unusual patterns, unauthorized access attempts, and potential security risks. Continuous monitoring is instrumental in maintaining a proactive security stance and preventing sophisticated attacks.
Also read: Top 10 Cybersecurity Training Options
Compliance Adherence
Many industries have specific cybersecurity regulations and compliance standards that businesses must adhere to. Cybersecurity experts are well-versed in these regulatory frameworks and ensure that the business complies with legal standards. Compliance adherence not only mitigates the risk of legal penalties but also increases the overall trustworthiness of the business in the eyes of customers and partners.
Increasing Customer Trust
Customers want to know their data is safe. By prioritizing cybersecurity, you show them you take their privacy seriously. This leads to happier customers, stronger loyalty, and a better brand reputation.
Tailored Security Strategies
Every business is unique, with different digital assets and risks. Cybersecurity experts don’t offer a one-size-fits-all solution. They assess your specific needs and create a custom security plan just for you.
Future-Proofing the Business
Cyber threats are constantly evolving, but cybersecurity experts are always one step ahead. They anticipate future risks and adapt your defenses accordingly, ensuring your business data remains safe.
Endnote
The benefits of cybersecurity hiring extend far beyond mere technical expertise. You can protect your company and its priceless assets from potential cyberattacks by putting strong cybersecurity measures in place and keeping up to date with the newest threats and technologies. In the battle against cyber threats, having the right experts on your side can make all the difference.









Leave a comment