Security
Best Network Troubleshooting Tools 2026: Ultimate Fix Guide
Finding solutions to network issues is an important primary element of a network administrator’s task description. Every administrator will be equipped with a...
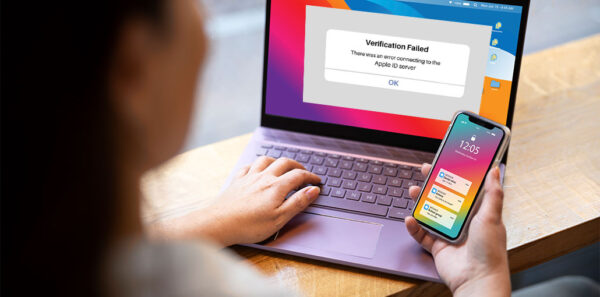
ByAiden NathanMarch 28, 2026Error Connecting to Apple ID Server? 9 Easy Fixes That Work
Suppose you encounter the ” There was an error connecting to the Apple ID server” prompt on your screen, but do not know...
ByBarrett SMarch 26, 2026Reset Mac Password: 5 Easy Ways to Unlock Your MacBook
Due to the strong security features of Apple’s latest macOS operating system, there’s an increased focus on data security. When you’re logging into...
ByBarrett SMarch 9, 2026Why Delete Is Not Enough: The Business Case for a File Shredder Software
Data is an important asset, but it can also be a massive liability if handled improperly. According to the 2025 IBM Cost of...
ByBarrett SFebruary 27, 20265 Critical Mistakes Companies Make During Incident Response (And How to Avoid Them)
Most incident response failures don’t start with a sophisticated attack. They start with confidence. A plan exists. Tools are deployed. The SOC is...
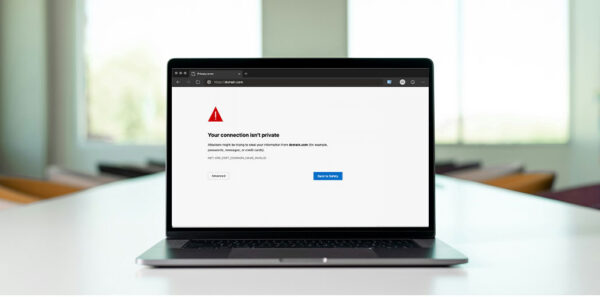
ByAiden NathanFebruary 13, 2026How to Fix Your Connection Is Not Private Error in Chrome
Learn and comprehend the various ways to fix Your Connection Is Not Private Chrome Error in this guide: Compromised privacy is the most...
ByBarrett SJanuary 13, 202610 Best AdBlock VPNs for Fast, Secure, and Ad-Free Browsing
AdBlock VPNs are the best way to protect your online privacy and security. Surfshark VPN, NordVPN VPN, and CyberGhost VPN, to name a...
ByBarrett SDecember 17, 2025DNS Server Not Responding: 11 Simple Solutions Anyone Can Try
The message “DNS Server Not Responding” in your browser can be an unpleasant experience. The error indicates that there’s something wrong with the...
ByBarrett SDecember 2, 2025Best VPN for Torrenting 2025: Top 6 Picks for Privacy
The article below has tried and evaluated the best VPN for torrenting in November 2025. Torrenting is a method of sharing files. It...
ByAiden NathanNovember 27, 2025Top 10 Dark Web Monitoring Tools to Prevent Data Leaks
Companies looking to stay ahead of security breaches and Data leaks can benefit by using Dark web monitoring tools. They look for personally...
ByAiden NathanNovember 24, 2025