Search Result for: Security Practice
8 Cybersecurity Tips for Online B2B Interactions
When you work in a B2B environment, cybersecurity is especially important for the overall health of the company. As such, managers and employees...
ByDelbert DavidFebruary 4, 2023What is Cloud Security and How to Secure the Cloud Computing?
Many types of businesses are now using cloud service providers as their standard model for cloud computing. Cloud-based software models have many advantages,...
ByDelbert DavidJanuary 19, 2023How To Secure Source Code and Protect It: Best Practices
Source code is a valuable asset for any company. If it is stolen or leaked, this could cause huge damage to your company....
ByDelbert DavidDecember 4, 20225 Biggest Cybersecurity Threats to Watch Out For In 2022
With the onset of the new year, we are reviewing the most significant challenges people will face globally. Cybersecurity falls within that category....
ByZoey RileyNovember 19, 2022What Is Container Security: A Complete Guide
Why is Container Security? Organizations must assess the attack surface of their systems to determine if there are any vulnerabilities. Security threats and...
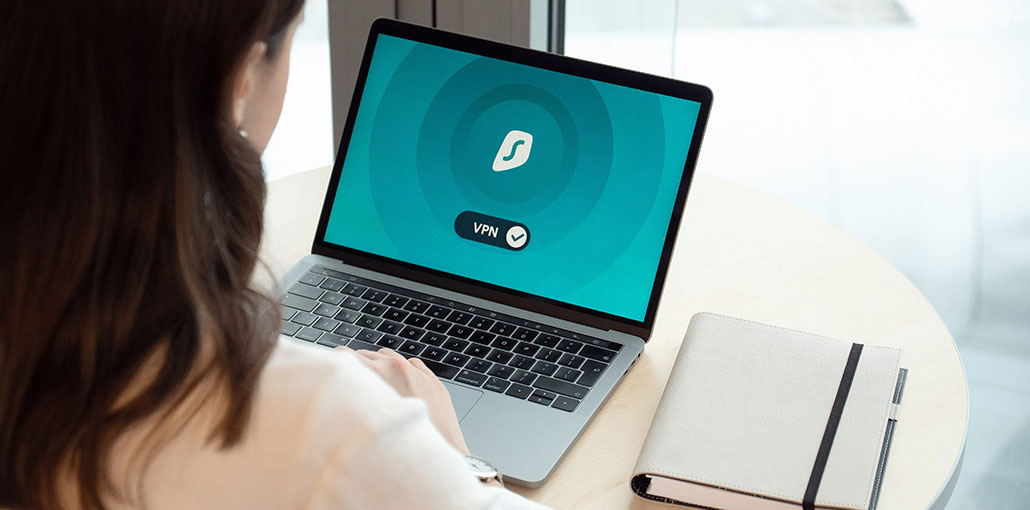
ByBarrett SOctober 24, 2022How Does VPN Amplify Your Online Security?
In the context of the World Wide Web, a major revolution has been witnessed in the last five years. Whether I conclude Cybersecurity,...
ByZoey RileyOctober 17, 2022What is Threat Modeling: Practices, Tools and Methodologies
What Is Threat Modeling? Threat modeling is a structured method to identify potential threats and prioritize security mitigations. Any cybersecurity team must perform...
ByBarrett SOctober 14, 2022New Hospitalist Practice Management Software in 2022: 9 Reasons to Invest
Hospital and facility-based medical specialists are the fastest-growing specialties in medicine. The biggest subset of the mobile medicine trend is hospitalists, a new...
ByBarrett SOctober 12, 2022Email Thread: What It Is, How To Forward It, Best Practices
We have all been in this situation This is where you’re looking through your inbox for a specific email about a project. It...
ByDelbert DavidOctober 11, 2022Top 10 Cybersecurity Training Options
It is imperative that you are prepared for any security incident, especially as small businesses are increasingly being targeted by cyberattacks. Cybersecurity training...
ByAiden NathanSeptember 25, 2022