- Remotely install, remove or delete the software from employees’ devices.
- Employees must assume that all they do on the computer at work is being monitored and recorded.
- Although many people have access to their non-work accounts from their work computers it exposes their personal information to the IT department.
- Privacy is a common expectation when it comes to technology. But, this is not the case when it comes to technology at work. Your work devices may not be as private as you might think.
Most businesses won’t have access to your data unless there is a reason to believe you’re not as productive as they should. However, you can assume that you’re being watched in some way Employers can access every file, every website visited, and every email sent with the help of employee monitoring software.
Clearing your browser history and deleting a few files won’t prevent your computer from showing your internet activity. Here are seven signs that your computer at work is leaking your private information.
1. Emails are not as private and confidential as you might think.
Many companies store all emails indefinitely. This may be something employees don’t realize. For various reasons, organizations may search their mail archives for discovery related to a case. A newspaper may request that a government agency conduct search warrants. The search might uncover emails that are not related to the request, such as personal emails.
Also read: How to Leverage & Implement Employee Monitoring Software
2. Clearing your browser history will not help.
An employer can monitor an employee’s internet use easily and provide reports to them. All outgoing network traffic flows through a firewall or router that allows that capability. Your computer is connected to your local area network (LAN) when you’re at work. A firewall is a device that connects to the company LAN and the internet. It provides security. It controls network traffic outbound and restricts inbound access to websites.
3. Your phone is not your private.
“Most companies have some type of internet filter. Barracuda’s Web Filter appliance can monitor all internet activity on any computer or device connected to the network.
4. Remote workers, beware! Your location is visible.
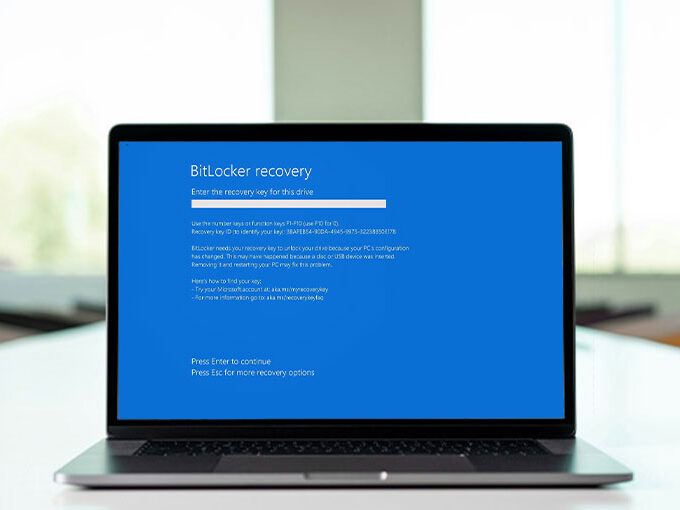
Many large IT companies, such as IBM, offer mobile management tools, like MaaS360 that allow employers to control their employees’ devices. Employers can remotely wipe out employee devices that were used to access company information or install or remove the software.
There is no argument that company-owned devices are safe. However, employee mobile device usage policies can also be used to enforce the appropriate use policies and end of employment data removal policies for employee-owned devices. Because BYOD is so prevalent in today’s business environment, mobile devices are often stolen or lost. We can quickly access company resources or scrub data from these devices in such cases.
Sometimes false alarms can be resolved easily with the remote tracking capabilities in mobile management software. One day, a client called our support desk to report the theft of a notebook PC. We used MaaS360’s GPS tracking feature to locate the notebook at the counter at the opposite end of the building, where it was mislaid by an employee.
5. Employers can track every word that you type.
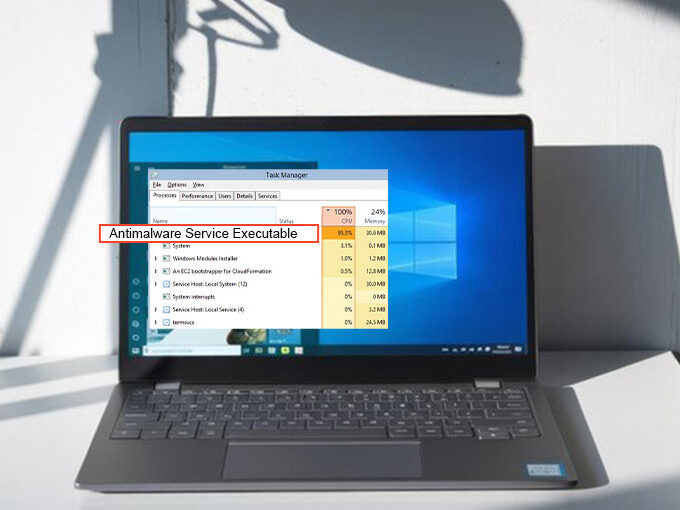
Employers can install a variety of applications on their employees’ computers, which are basically hacking programs. Employers and vendors consider these ethical hacking tools if they are legally used. These programs can be used to protect against employees sending out lists of Social Security numbers or credit cards.
These programs can upload real-time activity to a cloud console to be reviewed by the employer. This includes browsing history, screenshots every X minutes when an Excel or Word document is opened, keystrokes, and screenshots of emails that were opened, to name just a few.
6. You could monitor your productivity.
“We have employees around the globe. After a few bad experiences, we tried to find a way to track what our employees do while they are logged in during work hours. All out-of-office employees are required to use TimeDoctor.com. We keep track of screenshots, time per project, and time per software.
Webcam shots are also tracked. An email is sent to our team leader in the event of low productivity. The software is well-known by the workers, and productivity has increased significantly since its implementation three months ago. Some workers may not want to use tracking software. That is okay with me. It helps me to eliminate unscrupulous workers.
Also read: 10 Tips Virtualization Can Improve Security
7. Every file that you access is visible.
“Working from a Server? We have all the files you’ve uploaded to the server and when. There are many other ways to do this, but clients often ask me if my boss can see what I am doing. The answer is always “Yes.” – Justin Esgar CEO, president, Virtua Computing
You shouldn’t do certain things on your work computer
Many businesses use monitoring software in order to monitor employees’ computer activities. This may surprise some employees. Employees should not use their work computers for any other activities than those required by the job.
Employees should never do three things on a computer at work
- Protect your personal passwords. Many people have access to their accounts from non-work computers. You are taking the risk by sharing personal information with IT staff. Encrypted transactions are not impossible to access. Hackers can gain access to your personal information quickly if they have the right tools and knowledge.
- You can do any other activities that are not work-related. You only have one purpose for your work computer. If you are caught using your computer for non-work-related activities, it will make you look unprofessional.
- Search for jobs. You could be fired by your employer if you find out. This can also cause problems with your relationships with your supervisors, and the human resource department. Who can trust an unethical employee?
Your employer may also be willing to give references to prospective employers if they reach out to you.
It is best to think of your laptop as a borrowed computer. Consider whether your employer would approve of the content that you are browsing. If your answer is “No”, then you shouldn’t be doing this on company time or equipment.
What to avoid on a computer at personal work
- Write sensitive emails. Your personal email address should not be used at work. Employers may use keystroke tracking and you might be receiving messages that you don’t want your boss to read.
- Talk about your strong opinions in company chats. This is an important rule to remember. Employers can not only see what you have typed in company chat but they can also see the chat log.
- Personal files should be kept on the company computer. Do not save or share personal files to the company’s desktop. These files can be easily accessed. Do you want your boss to see everything you have saved?







Leave a comment