If you use Google, you might have faced its annoying security alerts. You may have even tried to disable it or take some other measures, but you keep receiving it again and again. At some point, this issue may raise a question if these Google security warnings really mean something?
Why Would Google Send Me a Security Alert?
The service invented the alert message for notifying their customers when they suspect some strange actions on their accounts. They may include the use of unreliable or leaked passwords, the absence of certain security features, and others. This actually is a very useful service because every day there appears new methods of system breaking, bugs, etc.
What is the most common cause for a critical security alert Google would inform you of? For example, you are trying to sign in to your account from a new device. However, there are cases when unusual activity in your account is real. You can track it if you use reliable security software like VeePN. However, not always a security alert is true. Let’s go further.
Also read: 5 Tips to Protect your Network from Malware Attacks
Is a Google Сritical Security Alert Real?
Security notifications are definitely a great thing. Sadly, some Google security alert scam still exists. Those who need to get your information realize that if they create a true copy of Google’s notification, you will most likely click on it to check what’s going on thus letting third parties access your private information.
This is, of course, a big deal. Even Google says hackers keep making attempts to get people’s information using replicated security alerts. Basically, the company confirms its customers have become victims of Google’s critical security alert scam.
What Will Happen if You Swallow the Bait of Scammers?
Let’s say you received an email from Google. Someone knows your password which is a scam. If you did open the suspicious email, clicked the link from the email, or downloaded something to your device, you have to keep in mind that:
- Scammers received your passwords
- They might have installed malware or spyware to your device to use it in the future
- Scammers may steal information stored on your gadget
- They may start sending you tons of unneeded ads
This is not all that hackers can do if they get access to your gadget. But this is still not a reason to panic. There exist methods that will help you get rid of this kind of scam.
What Should You Do if You Get One of Those Security Alerts?
Google security alerts will hardly surprise anyone. However, being aware of possible scams, you need to take several steps:
- Ask yourself: is the Google security checkup legitimate? There is nothing wrong with using a VPN or log-in to your account from another gadget. If this is what you were doing when you received the alert, this is definitely a false one.
- Examine the sender of the email with the security alert. If it is an email ID with a no-reply mark from Google, you don’t have to worry about it. If it is something else, never open this email.
- Pay attention to the quality of writing. An email from Google will not contain any mistakes and will be written in a formal style. If the email you received does not look that way, it may be a scam since hackers would not bother about the writing style or grammar.
- Links and Download buttons are a bad sign. If there are any of them in the email you received it is most likely spam. Google applications include all these options so they don’t ask you to do it from an email.
- Use Security Checkup
Google has a special Security Checkup page where you can see detailed information about your account. it will help you define any suspicious activity.
Also read: How to Protect Yourself Against Ransomware
How Do I Fix Google Critical Security Alerts?
You have to remember that in such situations the most important thing is acting fast. In case you suspect something strange going on with your account, please, do the following:
Change all the passwords you have
Clear your cache to delete all information, including passwords, from your browsers. You will need to change all your passwords as quickly as you can. Remember to use different passwords for different accounts.
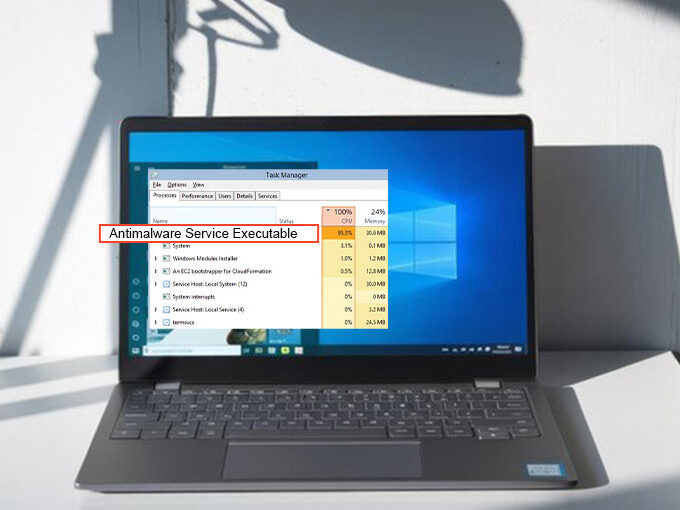
Launch scanning on your device
As it was mentioned above, hackers, after breaking inside your device, may install some harmful software. This is why you need to be sure you’ve got a powerful antivirus program on your device that will help you with all the possible spyware.
Launch ID Theft Protection Program
We would like to emphasize that you should not keep your personal information on your device. You may want to install ID theft protection software to check your device from time to time to see if any of your personal information is kept there. If found, the software will help you manage it.
We understand that no one wants their personal information to be hacked. If you follow the tips described in this article next time you see Google security warnings, you will be able to prevent the theft of your credentials. And, of course, avoid keeping important information on your gadgets.









Leave a comment