The smart home you live in is an amazing technological marvel. However, with cameras that could be compromised to monitor us, microphones controlled by lasers, and whole security systems that could be compromised by the connected smart device, it’s not surprising to be hesitant about connecting your home online.
There’s no reason to ignore the advantages of smart home appliances completely However, it is important to be aware of the risks. The key is to be aware of the dangers and make use of the security options available. No matter if you’ve got a whole collection comprising smart kitchen appliances, or a one voice assistant, take these steps to make sure that no one gets your equipment.
1. Consider What You Actually Need
Before rushing out to buy a smart thermostat, smart speaker or video doorbell take a look at your level of comfort in keeping in mind security and privacy. A security camera may provide security, but are happy with your video being uploaded online? A voice assistant like Alexa never sleeps, always listening to your commands. Do you think that’s creepy or just a benefit? Determine what you require from a smart house, and when privacy is more important than convenience for you.
Also read: Top 22 Smart Home Gadgets For 2023
2. Secure Your Wi-Fi Network
From the beginning, the majority of routers utilize an individual model-specific SSID and are either not secured or use a standard password such as “admin,” making it easy for hackers to gain access to your Wi-Fi at home and look through your connected devices.
The first step is to secure your Wi-Fi network by using an effective password. If your router supports it, think about changing the SSID which is the name of your Wi-Fi router.
When you’re there, be sure you’re using the highest security protocol. Most of the time, WPA2 will be your best option, but the latest routers will use the more secure WPA3 standard.
3. Update Firmware
Firmware is the software that runs your and other Internet of Things (IoT) devices. You can use the firmware of your router to alter the password, as well as configure different options.
Companies release bug fixes and other new features via the internet to various connected devices. Many automatically update after connecting to WiFi. The registration of your smart gadget with its manufacturer could assist in making sure these updates get to your devices.
There are many devices that require their owners to actively select the Update button to get the most current security and features patches. Do not ignore these as running outdated firmware versions can make devices vulnerable to hackers seeking to exploit flaws that aren’t patched.
Set up your device to automatically update if you’re willing to take the possibility of risk associated with automated downloads from servers of third parties. If not, the best option is to set a timer to periodically check for changes. Amazon, Arlo, Google, Ring, Wyze, and many others offer information on how to update and check your firmware.
4. Replace Outdated Routers
You probably purchased an upgraded laptop or phone within a few years. What about your router? It has been sitting on a desk for too long? If your performance on the internet isn’t sagging and your security isn’t compromised, then the security of your devices is. A sagging router translates into outdated security protocols and an easier access point for criminals.
If you’re looking for an upgraded router, the latest home internet standard is Wi-Fi 7. Certain brands have started to roll out new WiFi 7-powered routers. As you wait for more options to become available you can take a look through our reviews of the top Wireless routers and gaming routers along with Wi-Fi mesh networks.
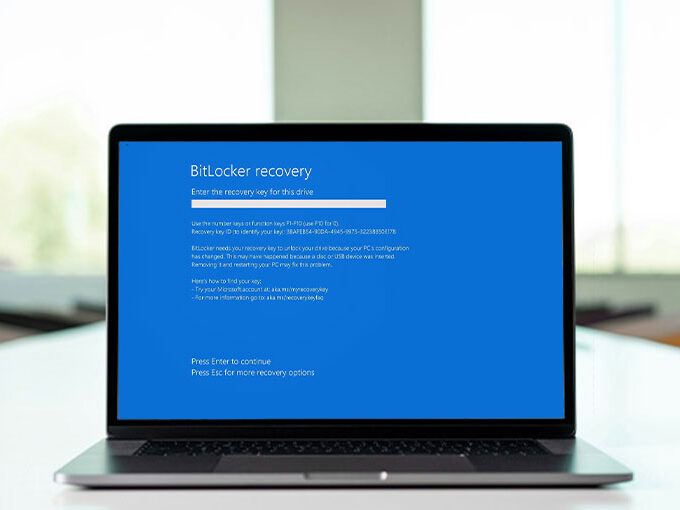
5. Manage Your Account Passwords
Once the Wi-Fi network is secured it’s now time to safeguard the devices and services connected to it. A lot of smart devices are controlled by a mobile app and you’ll have to create an account for each.
The same password to access every account is convenient, however, it’s also a security hazard. If one of the accounts is compromised and the password is exposed, hackers could have access to all other accounts where you utilized that password. Create your own unique password that you remember, but other people won’t think of. You might choose to employ a random password generator in order to create difficult-to-guess passwords and a password manager to store the passwords for you.
6. Enable Multi-Factor Authentication
Strong passwords are an aspect. However, there is a way to take this one step further by activating multi-factor authentication (MFA) for supported services. In the event that an attacker gains access to your username, they will not be able to access your account unless you have another method of authentication.
Check the security settings of the accounts you’d like to secure and begin using an authenticator program such as Google Authenticator or Authy (SMS-based authentication is also an option however it’s generally seen to be less safe than authenticator apps). After you’ve logged in, the accounts you want to protect will require a password and a second type of authentication, such as the six-digit code generated by the authenticator of your preference.
Many smart home devices support MFA, including Amazon Echo, Arlo, Google Nest, Ring, and many more. Learn more in our guide on the platforms that support it, and how to configure it.
Also read: The Impact of Artificial Intelligence In Smart Home Automation
7. Split Up the Network
A new FBI advisory suggested that “your refrigerator and laptop shouldn’t be connected to one network. Make sure to keep your most private and sensitive data on a different device from other IoT devices.” Since hackers don’t care if you’re low on Greek yogurt. Your refrigerator’s security is merely an access point to break into your Wi-Fi network and steal information from your laptop or mobile.
You can avoid this by setting your appliances on several networks. Many routers allow the setting up of a second guest network that can also be used to connect smart home devices. This is not just freeing bandwidth for browsing and streaming, it also can be a way of separating IoT devices from information that you want to secure. If you get compromised and infected with malware, that is affecting your smart home devices will not take over and harm other devices on your network.
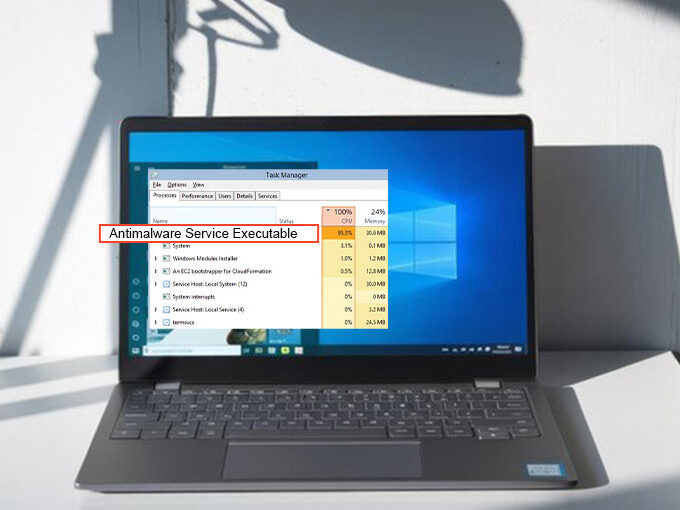
8. Monitor Your Network
If you’re still worried about the security of your network You can monitor manually the Wi-Fi users. The application Wireless Network Watcher For instance, shows all devices connected to your router, so that you can check them against your own devices.
To protect your network from weaknesses, we suggest purchasing a complete security program to guard against anything a malicious user could try to infiltrate your network.
There are, however, gadgets that check your network for weaknesses: Firewalla sells products that let you see and control all devices on your network as well as their activities. (We awarded Firewalla the Firewalla Purple our Editors’ Choice distinction.) Also, there is the Fingbox which is able to detect security holes, block suspicious items, and so on.








Leave a comment