The development of the internet and easier access to it have permanently changed the lives of the vast majority of users. Using the web has more common than using other media, it provides us with entertainment, access to information, shopping, and even financial transactions.
There are so many benefits of the internet that it is hard to think of its weakness or even flaws. Unfortunately, alongside the positive effects, new threats appear from time time.
Internet Threats Types
Harmful phenomena on the Internet are especially dangerous for children and adolescents because they spend the most time there and often find it difficult to defend themselves. On the Internet, nothing is lost, and the effects of these phenomena may be long-term and manifest themselves in many fields: physical, mental, or cognitive. Therefore, the key to protecting children and young people online is education and awareness of how to care for safety.
Internet is one of the inventions that changed our reality beyond recognition. And although the Internet should definitely be assessed positively, there are many threats here, especially for inattentive users or children. These include:
- Dangerous content
- Harmful relationships and cyberbullying
- Scam and phishing
- Fake news and hate
- Internet addiction
- Hacker attack
Internet threats target both individuals and businesses. Corporations and startups. International actors and local companies. In general, companies that can harm and know how to do it – and you can lose a lot, which you do not want to see the hard way. In order to effectively defend against them, you need to know what may threaten you and what methods can be used.
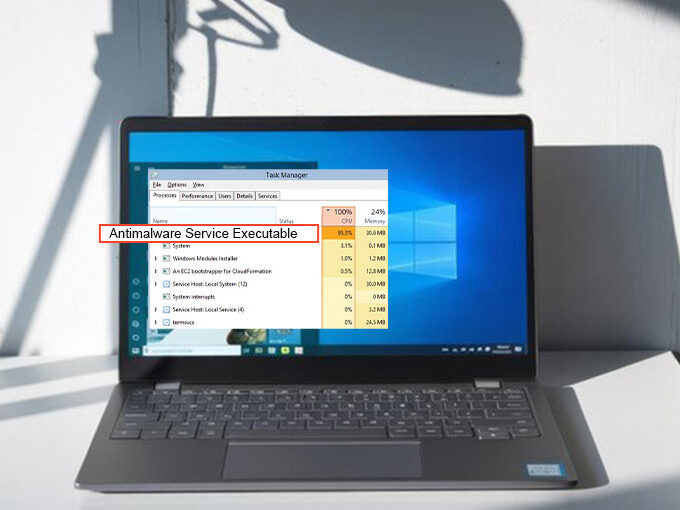
1. Antivirus software
Threat detection and management software can cost a lot, but there are many free options a personal user can take advantage of. Big brands such as Kaspersky, McAfee, and Symantec offer free versions. Such services provided include data loss prevention and automatic backup, as well as anti-virus, anti-spyware, firewall, and privacy protection.
The best antivirus programs are able to recognize and neutralize various types of malware: not only popular Trojan horses and viruses but also software that tracks user activities and logs keyboard activity or displays unwanted, intrusive advertisements as well as software ransomware.
Also read: 10 Advantages of A VPN You Might Not Know About
2. Don’t click on suspicious links
One of the simplest forms of extorting personal data and money from Internet users are colored links that appear right after entering certain websites. A person who does not know about the threat will certainly click on such a link. This can generate negative consequences.
Clicking on pop-up windows that are unrelated to the content on the site or some legal solutions are usually viruses. After accepting such a link, we may virus our computer or phone. The hacking software will then download the data and then use it to hack into the account of our social networking site, bank account, or instant messenger. Therefore, the basic principle of being on the Internet is extreme caution. We do not click on links under any circumstances,
3. Avoid using public Wi-FI
Wi-Fi networks If you do not have to, then do not connect to the Internet via public, generally available Wi-Fi networks. Under no circumstances should you provide your confidential data then – do not log in to online banking systems, e-mail, or various types of transaction services.
Do not make transactions and log in to websites using public and open hotspot networks, e.g. in McDonalds or on buses. The probability of intercepting sensitive data in such networks is very high.
4. Use strong passwords
Passwords are your primary and, in fact, the most important security. Do not go the easy way in this regard, for example, do not add the same password everywhere, e.g. the date of birth or the name of your pet. A strong password is definitely better security.
5. Two-step verification
Where verification is necessary, for example with online payments, it must be verified in two steps. So in addition to logging in to a given page, set yourself, for example, a code received in an SMS message. A potential thief with a high probability will not be able to make purchases without your will.
6. Don’t forget to log out of websites
After you have finished using the website that requires logging in, you should immediately use the logout option. This is especially important when using networks shared with other users – e.g. at school, work, or library. By logging out, we reduce the risk that confidential data will be taken over by a third party.
Also read: How to keep your online transaction safe
7. Regular backup
Making backup copies protects you not only against internet threats but also against system failure and damage to your hardware. It is best to perform backups in accordance with the 3-2-1 rule, which consists of creating three copies, storing them on two carriers, one of which is stored in a different location.
8. Protect all your devices
If you log into the network on various devices – not only a computer but also a laptop or tablet – then the protection of the computer itself may not be enough. Netia users can protect their mobile devices against Internet threats using the Safe Smartphone service.
In Conclusion
There are many more attack methods and techniques used by cybercriminals than those mentioned above. By following all of the guidelines discussed in the post, you still cannot be 100% guaranteed that your corporate and private data will remain safe. Hackers are constantly looking for new ways to break through firewalls and steal valuable information. Nevertheless, by not having an antivirus, not creating backups, not having a strong password, and not updating your software, you let your guard down and become an easy target.









Leave a comment