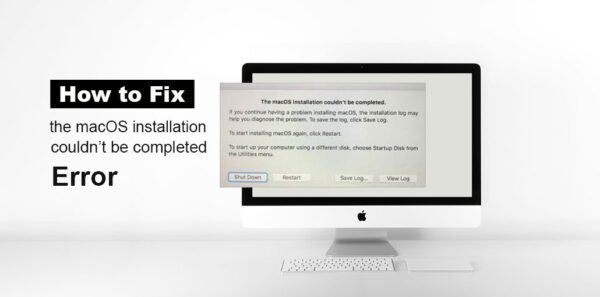
The macOS Installation Couldn’t Be Completed: 6 Proven Fixes That Work
If you receive the error message “the macOS installation couldn’t be completed” while trying to upgrade macOS What should you do to resolve...
ByBarrett SMarch 31, 2026WiFi Connected But No Internet? 7 Easy Fixes for All Devices
It’s frustrating to get the ” WiFi Connected but no internet Connection ” message. Particularly when you are using the internet connection to...
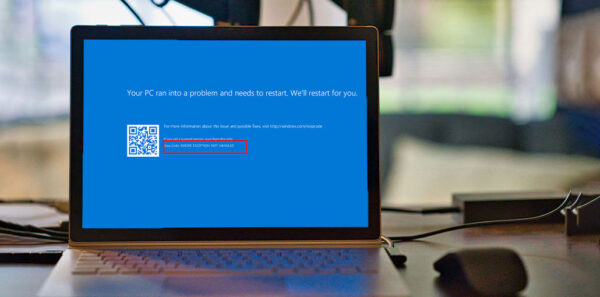
ByIsla GenesisMarch 30, 2026KMODE Exception Not Handled Error in Windows 11/10: Ultimate Fix Guide
Are you a Windows user experiencing problems with the “Kmode Exception Not Handled” error? If so, this article is ideal for you. The...
ByBarrett SMarch 30, 2026Fix Preparing Automatic Repair Error in Windows: 10 Quick Solutions
“Preparing Automatic Repair” error occurs when users turn on their computers and attempt to start up Windows. The error may occur after a...
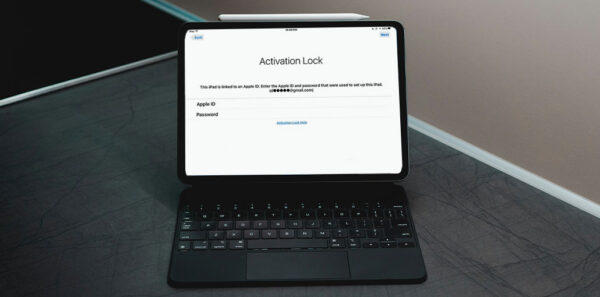
ByIsla GenesisMarch 29, 20265 Best iCloud Activation Lock Removal Tools in 2026
Have you ever experienced the iCloud Activation Lock on your iOS device and been unable to access it? In this article, we’ll go...
ByBarrett SMarch 29, 2026How to Fix GPS Not Working on iPhone: 8 Quick Fixes for GPS Issues
Most of the time, the iPhone works perfectly for us; occasionally, it has issues with Wi-Fi, Bluetooth, and GPS. Recently, iPhone GPS issues...
ByIsla GenesisMarch 28, 2026Best Network Troubleshooting Tools 2026: Ultimate Fix Guide
Finding solutions to network issues is an important primary element of a network administrator’s task description. Every administrator will be equipped with a...
ByAiden NathanMarch 28, 2026How to Free Up iCloud Storage on Mac and iPhone: 5 Best Methods
Finding that your iCloud storage is stuffed, however, there’s no reason to panic. Before you commit to a costly upgrade, you’ll be amazed...
ByZoey RileyMarch 27, 20267 Best Options for Buying Real-Time Communication Systems
Real-time communication systems are designed to deliver information between people the moment it matters. The environments where these systems are needed most tend...
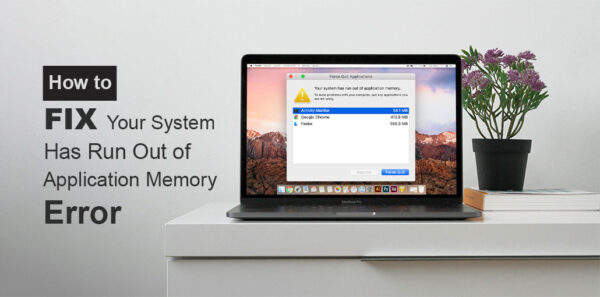
ByAiden NathanMarch 27, 2026Your System Has Run Out of Application Memory on Mac? 11 Easy Fixes
Perhaps you’ve recently experienced an error message that reads “Your system has run out of application memory” displayed in your Mac. Any error...
ByAiden NathanMarch 26, 2026