2020 was a year of accelerated transformation as organizations hastened cloud-service adoption to encourage a sudden transition into remote work. The transition rate demonstrated an impressive amount of adaptability, but in addition, it left some establishments vulnerable.
Security protections were frequently skipped at the hurried movement to cloud-based services, and poor actors haven’t hesitated to take advantage of this circumstance. By way of instance, account production attacks skyrocketed from the very first months of lockdown from the U.S.
As they continue to quicken their cloud transformation in 2021, ready organizations will take action to strengthen security and safeguard their sensitive information from breach or compromise. Securing systems from the cloud demands different strategies and strategies, and the two IT teams and basic staff will have to adjust.
Here are just three best practices to remain on top of evolving risks and flourish in a cloud-based landscape.
1. Offer Cloud Security Training
After the pandemic struck, authorities immediately transitioned workloads into the cloud, however, present data center infrastructure frequently was not enough. Rather, companies needed to hurl workloads at outside cloud suppliers which were capable of incorporating capacity fast. This arrangement is still comparatively new, and lots of companies are still playing catch-up concerning the cloud experience they have to handle it efficiently.
That is particularly true in the domain of cybersecurity, as cloud safety abilities are equally in-demand and hard to employ. In 2018, a majority (53 percent ) of all IT decision-makers had difficulty hiring applicants with the necessary skills to encourage cloud initiatives, based on an AWS Academy research. The pandemic and corresponding acceleration of cloud conversion have probably surpassed the abilities gap.
In 2021, associations must solve to close that gap by investing in education, training, and certificate for existing workers as opposed to relying solely on hiring. This might be challenging for IT departments that lack expertise running coaching programs, whether inside their teams or to get a wider employee crowd. But many creative alternatives are possible, such as:
- Covering tuition for Outdoor Instruction Applications
- Organizing lunch-and-learns where senior Staff members Discuss Experience
- Developing a mentorship program to Assist Expert development for junior Employees
- Hosting Contests, Such as offering a prize for Workers That Place a phishing email
The skills gap is not going away, and you can not address the issue with hiring independently. It is up to organizations to construct strong training pipelines to make sure their workers have the ideal security abilities to flourish in the new cloud-based future.
2. Embrace Inclusive Design
For many businesses, the change into the cloud requires reworking existing cybersecurity procedures. IT teams must take this chance to be certain the layout is inclusive, which means that the item works equally well for individuals of diverse sexes, ages, literacy levels, physical capacities, along with other traits. Designing your merchandise for addition is a decision we have to make.
If you do not believe in inclusivity, you hazard excluding entire population sections from using your product. The individual experience is varied, and we must ensure we are doing what we can to draw the entire variety of human scenarios when creating a product. This begins by bringing addition to product development teams to make sure as many varied viewpoints as possible to make a solution.
There is no such thing as a”regular” user, which means that your product groups will need to design for everybody. Study your leadership and staff and determine where diversity is missing, and biases could exist. To prevent excluding diverse inhabitants, use multi-layered safety protections, therefore users’ accessibility isn’t determined by using anybody’s alternative.
This endeavor will not only improve availability, though that is an important aim. More inclusive design is generally a greater layout, which makes for a smoother, simpler user experience all around. It is a worthwhile investment to earn 2021.
Also read: How To Secure Remote Work Tool With Out Impact Business
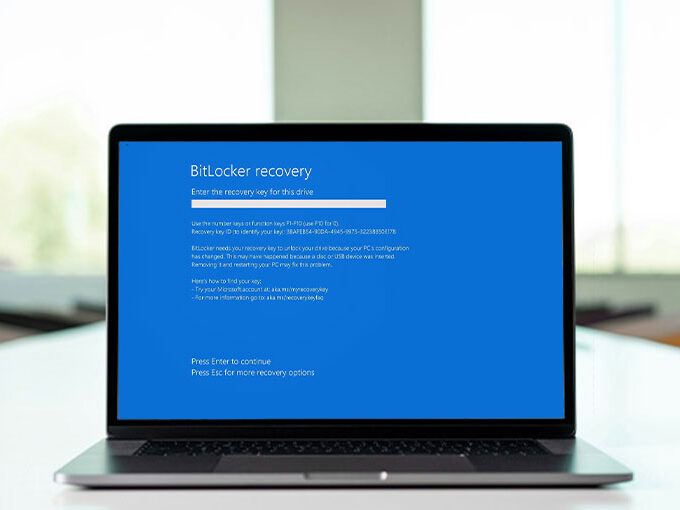
3. Don’t Trust Every Device
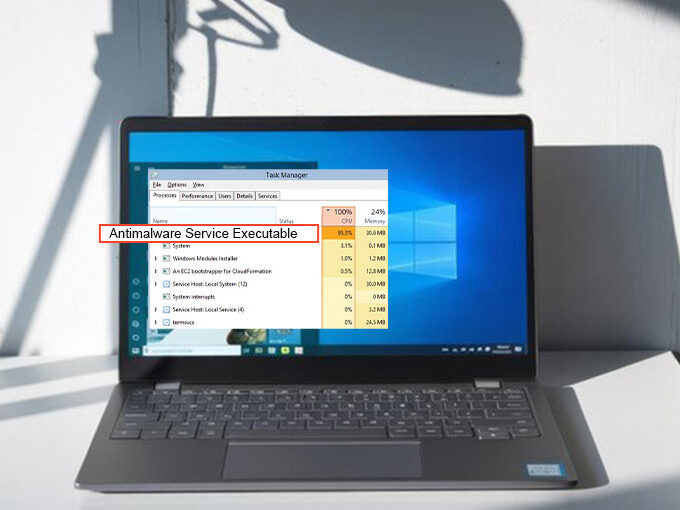
Since the amount of devices on the internet continues to grow exponentially, it is harder and harder for companies to understand which ones to trust. Information breaches have contributed attackers access to a treasure trove of information they could use to make false identities and apparatus, which may subsequently be utilized in a huge array of attack types, from fresh accounts fraud to denial of service (DoS) attacks.
And that confidence will continue to deteriorate if businesses do not become more complex about which apparatus to anticipate. It is a struggle to identify and limit”poor” users without creating tools hard or inconvenient for”great” users to get. By way of instance, safety rules which are too strict may deliver a helpful consumer CAPTCHA each time that they log in, dragging out login occasions and degrading the overall consumer experience. The challenge is increased by distant work since it is more difficult to determine valid users by their place at a specific workplace or employment website.
In 2021, businesses that are diligent about averting security snafus should solve to boost apparatus intelligence in a way that doesn’t include excess friction for end-users. By way of instance, passive biometrics appears at an individual’s inherent behavior — such as they hold their apparatus — to confirm their identity. Methods similar to this can assist your business trust the ideal devices even if users are on the go.
An Opportunity To Strengthen Protections
Following the chaos of 2020, the forthcoming season is a chance for businesses to take inventory of their cloud capacities and business infrastructure up and best practices to encourage those capacities in the long run. With strikes still on the upswing, you can not afford to sideline safety in this procedure. By investing in training, design, and apparatus intelligence, you are going to begin the year off by building a solid base for cloud safety later on.







Leave a comment