As companies transition into a digital era of rapid advancements and growing interconnectedness security has ceased to be an extra cost and has turned into a crucial requirement. The rise of digital business has boosted efficiency and increased accessibility but increased the risk of being a victim of a myriad of cyber-related threats. As the nature and severity of these threats, the idea of cyber resilience is more relevant than ever before.
Cyber resilience is the ability of an organization to sustainably deliver on its promises even in the face of adversity and cyber-related events. It’s not just about stopping cyberattacks however, it’s also about how the business reacts and recovers after such incidents do occur. The process of building a resilient cyber-security company is a process that requires careful risk assessment, the development of a comprehensive cybersecurity plan that includes defensive and proactive measures as well as a thorough and comprehensive training for your employees. Each of these steps requires attentiveness and attention to detail.
Risk Assessment
Every step towards cyber-resilience starts with a risk assessment. It establishes the basis for your plan by helping you comprehend your current situation as well as identifying vulnerabilities and the implications that could arise from a variety of cyber-related threats. In short, the risk assessment process consists of identifying your most valuable assets which could be targeted, including hardware software, data networks, and employees.
In the next step, you must determine the potential threats the assets could face and the vulnerabilities that might be exploited. These risks should be assessed and prioritized according to their magnitude. This process is cyclical and must be repeated often to take into account emerging threats, new assets, and identified vulnerabilities.
Also read: What are Cybersecurity Risks for ChatGPT and How to Mitigate Risks
Build and Manage a Cybersecurity Strategy
Once you have identified the potential risks Your next step is to develop a comprehensive cybersecurity strategy that minimizes these risks. The strategy you choose to implement should begin by conducting a gap analysis that compares your current security practices against the desired state. This is basically looking at your current security practices in relation to industry standards or frameworks like NIST as well as ISO 27001 to identify any weaknesses.
The gap analysis that follows is an extensive risk analysis, delving deeper into every risk that was identified during the risk analysis. This helps you understand how each of the risks works and helps you decide on the most appropriate responses.
As part of your strategy, you should create an emergency plan for backup and recovery. Regular backups can be instrumental in recovering data that has been lost or compromised in a cyber-attack. The plan should define the data that should be protected as well as the frequency at which it must be backed up, and the procedure for recovering data in the event of an emergency.
A solid cybersecurity plan incorporates an emergency response strategy that outlines your company’s response to cyber-attacks. It should outline who is responsible for what, how to escalate along with communication strategies, as well as steps to analyze and learn from the experience. In addition, regular cybersecurity audits is vital to evaluate how effective your security procedures are, discover security weaknesses, and help you make necessary changes.
Implement Proactive Cybersecurity Measures
A well-designed cybersecurity strategy should be proactive, always looking for and addressing potential risks before they become apparent. This means staying up-to-date with the most recent cybersecurity trends and threats. This lets you anticipate possible security risks and improve your security in the right way. Regular updates and patches of your applications and systems will prevent security weaknesses to be exploited.
The implementation of strong access controls is essential. ensure that employees have access to the information they require to fulfill their job to minimize possible damage that could occur in the event of an account being compromised. Furthermore, using Multi-Factor Authentication (MFA) adds an additional security layer by requiring more than just the password.
Implement Reactive Technical Defenses
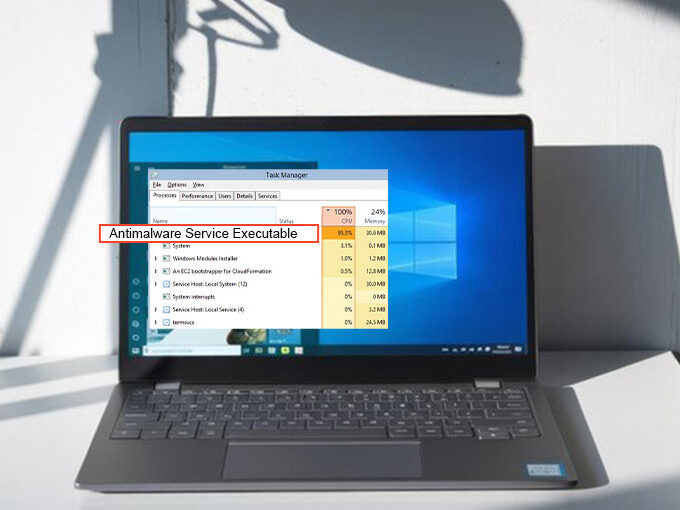
Despite the best efforts to prevent it the threat of cybercrime can infiltrate your security. Anticipatory defenses, such as firewalls and antivirus programs, can help minimize the harm when such incidents happen. Firewalls control and monitor outgoing and inbound traffic on networks based on established security rules, which are the initial protection against cyber attacks. Antivirus software is a complement to firewalls, blocking, detecting, and eliminating malware.
Intrusion Detection and Prevention Systems (IDS/IPS) keep an eye on your system for any suspicious activity and possible threats, advising the user of any potential threat and, in certain instances taking action to minimize the risk. encryption is a second useful and proactive method that makes your confidential data unreadable to anyone who does not have the proper encryption key, which protects your data in case it falls into the wrong hands. Security Information and Event Management (SIEM) systems offer real-time analysis and reports of security alerts that are generated by software and hardware in networks. They assist in detecting incidents earlier and swiftly respond.
Also read: 10 Best Security Awareness Training Platforms For Business
Employee Training
Human factors are usually the most vulnerable element in the cybersecurity defenses of an enterprise. Being aware of this, cybercriminals are more likely to target employees using tactics such as Phishing. Thus, thorough employee training is a crucial aspect of creating a resilient firm. Employees need to be informed of their responsibility in ensuring security through regular awareness training that covers the most common threats, safe online practices, and how important it is to have security procedures.
Based on their job depending on their job, certain employees might require specific cybersecurity expertise like knowing how to utilize security tools, recognizing and addressing particular threats, or handling sensitive information in a secure manner. Conducting regular exercises that simulate attacks, such as phishing drills, could assist employees to understand what a real threat might appear like and the best way to react.
Cyber threats continue to evolve and, as such, your training needs to encourage continual learning and be updated on the most recent threat and security. The process of building a resilient cyber-secure company is more of a journey than an endpoint. It requires constant work, education, and adaptation. But the rewards are huge: Not only does it protect your company from cyber attacks, but, it can also give you a competitive advantage. In a world that is becoming increasingly interconnected customers, partners, and investors are incredibly impressed by companies who take cybersecurity seriously.
Conclusion
In short Cyber resilience refers to the ability to continue your business operations in the face of adverse cyber incidents. It requires a thorough risk assessment, constructing an extensive cybersecurity plan using both reactive and proactive strategies, and informing your employees. By promoting a security culture across all levels, companies can protect themselves from threats, and create a sense of confidence with clients with the assurance that their private information is safe. In a time when data breaches are becoming more common, building a cyber-resilient company is an investment in the future of your business’s sustainability and prosperity.









Leave a comment