What is SOC Analyst?
A SOC analyst (security operations center) is an important role in modern security teams. SOC analysts are at the forefront of cyber defense and respond to cyber attacks as soon as they occur. Learn more about the SOC analyst role and its responsibilities.
SOC analyst job description
SOC analysts respond first to any cyber security incident. They are responsible for reporting on cyber threats to the organization and implementing any necessary changes.
SOC analysts have the following job duties:
- Vulnerability analysis and threats
- Investigating, documenting, and reporting on information security (InfoSec), issues, and emerging trends.
- Analyse and mitigation of previously unknown software and hardware vulnerabilities
- Preparing disaster recovery plans.
SOC analysts are the last line of defense. They usually work in a large security team alongside cybersecurity engineers and security managers. SOC analysts usually report to the chief information security officer of the company (CISO).
SOC analysts must be detail-oriented as they have to monitor many aspects at once. They must monitor the network and respond to any threats or events. The size of an organization will determine the level of responsibility.
Also read: The Ultimate Guide: How to Become a Network Security Engineer
SOC analyst career path
Security operations centers typically assign analysts to three to four tiers.
- Tier 1 support security analyst – receives and reviews alerts every day. To determine the urgency and relevancy of SIEM alerts review them daily. Triage is performed to determine if a security incident is actually occurring. Assists in the configuration and supervision of security monitoring tools.
- Tier 2 support security analyst – deals with real security incidents. Assesses incidents that have been identified by tier-one analysts. To pinpoint the affected systems and determine the extent of an attack, threat intelligence is used. Analyzes the running processes and configurations of affected systems. Performs in-depth threat intelligence analysis to identify the perpetrator, type of attack, and the affected data or systems. Develops and implement a strategy to contain and recover.
- Tier 3 security analyst – More experienced than a level 2 analyst. Responsible for responding to critical incidents. Performs vulnerability assessments and penetration testing to determine the organization’s resilience and identify areas that require attention. Examines alerts, threat intelligence, and security data. Examines alerts, threat intelligence, and security data.
- Incident response manager – Manages and prioritizes actions during analysis, isolation, and containment. They communicate to external and internal stakeholders any requirements for high-severity incidents.
5 Responsibilities of SOC analysts
SOC analysts make sure that security incidents are correctly identified, analyzed, and guarded against. They also investigate and communicate any findings.
1. Implement and manage security tools
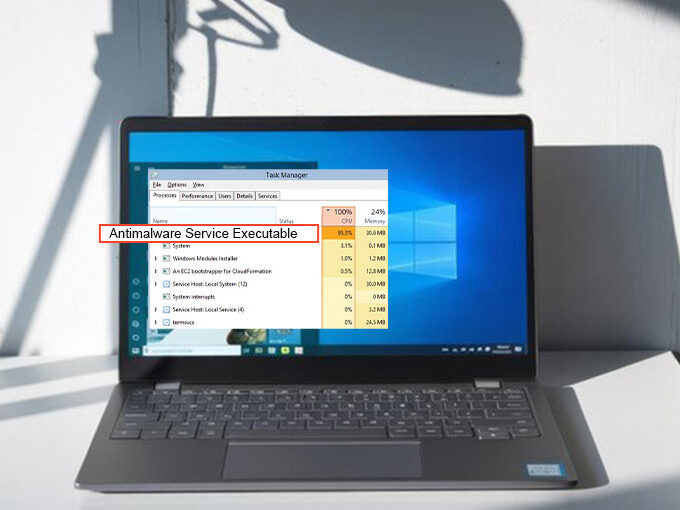
SOC analysts need to have access to technology products that give insight into the security environment of their organization. They should be certified or trained in the use of security tools and should be able to effectively operate them.
Firewalls, intrusion detection technology, threat management tools, vulnerability management tools, data loss prevention instruments, filtering technology, traffic inspection solutions, and reporting technology are all basic security tools. SOCs may have access to enterprise-level forensic tools to support incident response investigations.
A SIEM solution can also help to aggregate security events and generate alerts that analysts can use to investigate. The next-generation SIEM tools offer new capabilities such as user and entity behavior analytics (UEBA), and security orchestration automation (SOAR). These tools can help save time and identify threats that traditional tools cannot. Exabeam’s Security Operations Platform is an example of a next-generation SIEM tool that includes UEBA/SOAR.
2. Investigate suspicious activities, and contain and prevent them
SOC analysts use security monitoring tools to look for suspicious activity in IT networks and systems. They typically do this by analyzing and receiving alerts from the SIEM. These may include signs of compromise or related threat intelligence. Analysts respond to alerts and understand the severity of the threat. If necessary, they escalate the incident to higher-ranking analysts.
Although they may not be able to stop all threats from entering their network, SOC personnel can prevent them from spreading. If a network system is compromised, SOC analysts must identify infected hosts to prevent them from affecting other networks. Analysts can use switches, routers, and virtual local area networks (VLANs), to stop the threat from spreading,
SOC analysts must validate and correlate alerts in order to verify that they are relevant security incidents. An analyst’s role includes helping to understand the impact of events on the business network and coordinating responses with staff.
3. Reduce downtime and ensure business continuity
Companies need to ensure that their networks and systems are running smoothly. While it was possible to close down a mail server that had been infected with a virus for cleaning, this is not possible in today’s business environment.
SOC analysts must notify business stakeholders in the event of a security breach. As much as possible, security risks should be minimized before they reach the business infrastructure. If they reach critical systems, redundancy must also be in place to ensure business continuity.
In case of a breach, SOC analysts must notify the business stakeholders in advance of serious security incidents. It is important to minimize risks before they reach the business infrastructure. If they reach critical systems, redundancy should be in place in order to ensure business continuity.
Also read: How to Improve Your Security Posture
4. Providing security services to the rest of the organization
Ideally, SOCs function as shared service centres that offer value to business stakeholders and help them achieve their goals. SOCs are cross-functional organizations that centralize operations from different departments. This service is provided by SOC analysts.
An organization should empower its analysts to manage security incidents, monitor communication, and direct interactions with other IT, HR, legal, compliance, and other groups. Clear lines of authority will reduce confusion in critical situations such as the termination or shutdown of connectivity.
5. Audit and compliance support
SOC analysts often audit systems in order to comply with regulations for the government, industry, and corporate sectors such as HIPAA, SB 1386, and Sarbanes Oxley. Compliance requires efficient access to threat information and patch levels as well as identity and access control data.
SOC analysts used to use documentation templates in the past to create new documentation for audits. This is a time-consuming and error-prone process. Modern SOCs use security tools like the SIEM to gather security data across an organization. This makes it simple for analysts and analysts to create compliance audits or reports.
SOC analyst skills
These are the essential skills that all SOC analysts must have:
- Network defense – You must be able to defend your network. This includes monitoring, discovering and analyzing possible threats. A SOC analyst must have the ability to monitor and detect suspicious activity, as well as maintain secure network traffic.
- Ethical Hacking – Organizations must be able to identify threats and report them in a way that protects them from attack. SOC analysts must be able to conduct perpetration testing on systems, web apps, and networks in order to identify vulnerabilities.
- Incident Response – should be able to manage multiple effects of breaches in such a way as to reduce their impact. SOC analysts should be able to make recommendations to help prevent future security breaches.
- Computer Forensics – You must be familiarized with computer forensic techniques that can prevent cybercrime. This includes collecting, analyzing, and reporting on security data.
- Reverse engineering – You must be able to read and understand software program operation and performance parameters. A higher skill level should allow you to reverse engineer malware.
When cyberattacks are required, Tier 1 SOC analysts act as first responders. They review incident alerts and run vulnerability tests.
These are the most important skills that Tier 1 and Tier 2 analysts need:
- Tier 1 SOC analysts – must be proficient in administrative skills across multiple operating systems such as Windows, OS X, and Linux. Tier 1 SOC analysts can be proficient in many programming languages including Python, C# Java Ruby on Rails, and Perl. They are required to manage common security incidents on their own.
- Tier 2 SOC analysts – are also known as ‘incident responders’. They review tickets from Tier 1 analysts to determine if they represent serious security incidents that require in-depth investigation. The Tier SOC 2 analysts gather all the details necessary to assess the extent of a cyberattack and respond to severe attacks, and those that have a high business impact.









Leave a comment