Cybercriminals are a growing threat to businesses in today’s cyberspace. Businesses must be prepared to defend themselves against them. It all starts with identifying your weaknesses and understanding how your company could be compromised. Then, you need to implement the best prevention and detection methods that can help you build cyber resilience. First, you need to know what types of attack vectors you might face that could disrupt your business.
What is an attack vector in cybersecurity?
Cyber attackers use attack vectors or threat vectors to penetrate IT infrastructure. An attack vector, also known as a route or process that a malicious hacker uses in order to attack a target or other terms, is simply a method or route the hacker uses to get to the target.
Attack vectors are usually intentional threats, rather than unintentional. They require planning and analysis.
These vectors can be exploited by many entities, including former employees, hackers, cyber espionage organizations, competitors, and others. They may want to disrupt your business, steal technology, and confidential information, and extort money out of your employees, regardless of who they are. They will try their best to use attack vectors to gain access to your systems.
How are attack vectors and attack surfaces related
Attack vectors These are the methods used by cybercriminals to gain unauthorized access to a system.
The attack area refers to the maximum number of attack vectors an attacker could use to access or steal data from your endpoints or network.
The most common attack vectors in cybersecurity
Below are some examples of attack vectors that could threaten your company.
1. Insider Threats
One of the most prevalent attack vectors is the insider threat. However, not all insider threats are malicious. Sometimes, naive employees may accidentally expose internal data. Some employees may be motivated by personal gain and might deliberately disclose or plant malware.
According to the most recent statistics on insider threats, there are alarming issues that all organizations need to address. In the last two years, insider threats increased by 47% and 70% of organizations are experiencing more frequent insider attacks.
Also read: What are Advanced Persistent Threats and How to Prevent Them
2. Phishing Emails
Phishing is just one of the many hats social engineering can wear. This involves manipulating techniques used by a malicious individual whose ultimate goal is to trick employees into clicking suspicious links, opening malware-infected email attachments, or giving out login credentials.
Spear phishing is the most dangerous type of phishing. This involves extremely specific employees being observed in detail and then being targeted by cybercriminals. This is part of the growing threat of Business Email Compromise is a sophisticated and dangerous practice that can cause serious damage to companies of any size.
3. Supply chain attacks
Business partners are also potential vectors of attack in cybersecurity.
Vendors are responsible for some of the most serious security breaches and data breaches. Attackers can target vendors’ customers through supply chain attacks. Organizations large and small must work together to foster a culture of sharing cybersecurity best practices and demonstrating mutual transparency.
4. Weak or compromised login credentials
If your employees’ authentication credentials are too weak or compromised, it could be a way for an attacker to gain unauthorized access to your IT systems.
Passwords and usernames are the most common form of authentication. They can be easily abused by phishing, data breaches, credential-stealing malware, and other attacks that allow for easy access to accounts.
5. Brute-force attacks
A serious attack vector is the practice of attackers submitting multiple passwords in order to guess them. Heimdal Security’s data shows that brute-force attacks have increased exponentially in the wake of the new coronavirus pandemic. After the majority of employees started working remotely, we have seen a 5% rise in brute force attacks.
6. Unpatched vulnerabilities
Unpatched flaws in your system can result in exploits that allow attackers to gain access. If systems were patched promptly, the most famous ransomware attacks (like WannaCry or NotPetya), could have been avoided.
Ransomware is still a lucrative business for cybercriminals. Ransomware as a Service is a business model that has seen huge profits due to its immense profitability. This makes it accessible to anyone with a basic technical skill but who is determined to make a profit from the vulnerable users.
The large number of malware types available can also facilitate infiltration into your company by malicious hackers. Think about trojans rootkits, trojans, and spyware as well as file-less malware, bots, and other malware.
Keep in mind, however, that I have only listed a few possible vectors of attack that could affect your business.
7. Cross-Site Scripting
Cross-site scripting (XSS), a form of computer security vulnerability, is commonly found in web applications. XSS allows attackers to insert malicious code onto web pages viewed and accessed by others. Any malicious code infected by an attacker when a user views a page is executed by the browser. This can lead to the disclosure of sensitive information and the execution of unwelcome code.
8. Man-in-the-middle Attacks
Man-in-the-middle attacks are a form of cyberattack in which the attacker inserts himself into a conversation between two victims to intercept or alter the communication. The attacker intercepts the messages of the victim and alters them before sending them to the other victim. This makes it appear that the message was sent from the original sender. This attack can be used for stealing sensitive information such as login credentials and financial information. Man-in-the-middle attacks are also used to inject malicious code into websites and software. This can then be used by attackers to infect their computers.
9. DNS Poisoning
DNS poisoning (also known as DNS spoofing) is a cyber-attack where an attacker corrupts DNS to point a domain to the wrong IP address. This could lead users to malicious websites or servers, where they might be infected by malware or phished for confidential information.
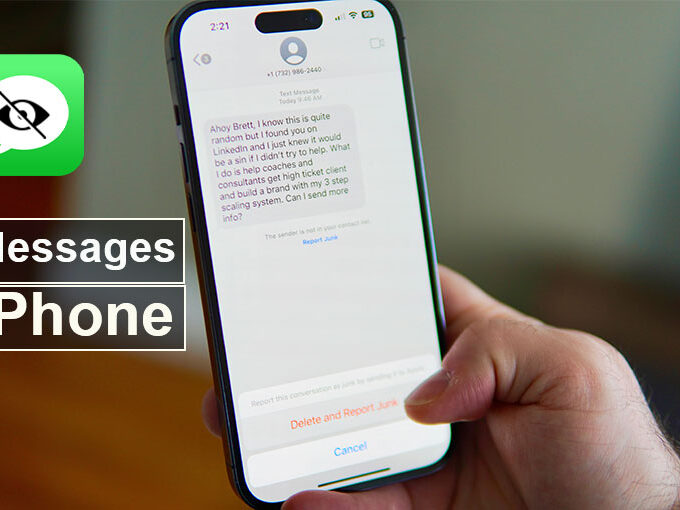
10. Malicious Apps / Trojans
Many malicious apps can infect your computer and steal your data. While some of these apps appear to be legitimate, others are clearly fake. Meta has compiled a list of over 400 malicious apps. These apps were listed in the Google Play Store as well as Apple’s App Store. They disguised themselves as photo editors, game, VPN services, business applications, and other utilities to trick people into downloading them.
Also read: How to Make Your Business More Secure
How to protect your business from threat vectors
With the right resources, protecting your business against different attack vectors is easy. Below are the key aspects that you need to focus on in order to decrease the risk of future attack vectors.
1. Educate your employees
We believe in continuous security education. This is why we recommend that all employees receive cybersecurity awareness training. As prevention is the key to keeping your company safe in today’s digital world, workers should continue to improve their cybersecurity skills. Cybersecurity training should be an ongoing process within your company, as long as cybercrime is profitable and continues to flourish.
Your employees must learn to recognize signs of phishing and BEC. They should also be taught how to create passwords based on their internal password policy. This will help them avoid common password mistakes and identify various types of malware. You can also teach them how to report cybersecurity incidents or potential threats. To help your workers recognize the warning signs of phishing, you can run phishing simulations.
2. Apply the Principle of Least Privilege
PoLP’s cornerstone is limiting your users’ rights to the lowest possible level that allows them to perform their tasks. This practice will close multiple security gaps within your organization. It also allows you to have granular control of the actions taken and eliminates the risk of insider threats.
3. Use a mix of cybersecurity tools for layered protection
Sometimes even the most qualified employees (cybersecurity-wise) may accidentally click on malicious links and open infected email attachments In some cases, cybercriminals can pose as employees’ superiors and other authority figures to trick them into transferring large sums of money to their accounts. Having the right cybersecurity tools can help you protect yourself against more attacks and reduce human error.
Summary Up
To evade threat vectors, Organizations must rely on cybersecurity education and tools for ongoing protection against threats.
It is crucial to adopt a DNS-based security approach that analyzes and monitors network threats, detects unknown malware, and can also be used to identify emerging threats. You can also eliminate attack vectors such as email, unpatched systems, and software, as well as manage admin rights to help prevent cyber threats from affecting your company.









Leave a comment