Software is an integral part both of commercial and private life. Software is required to book flights, do taxes, and browse the internet. The software has made our lives so much easier in many ways. But, software dependence can make us more vulnerable to cyberattacks.
This article will discuss 15 ways software can become a cybersecurity threat. These risks can be understood so that you can protect your business and yourself.
15 Types of Software Become a Cybersecurity Threat
1. Poor Password Security
Passwords that are easy to guess or weak can be one of the easiest ways for users’ accounts to get hacked. Use a strong password for programs that require you to enter it.
An attacker will only need to know one password to gain access to all accounts if you have the same password for multiple accounts. It is important to have different passwords for different services. To help you remember your passwords better, you can use a password manager.
To take advantage of the stronger security offered by these applications, you might consider using both a password management program and a password randomizer. This will allow you to generate long, unique passwords. Many password managers have a randomizer option.
Also read: Top 11 Enterprise Password Management Solutions
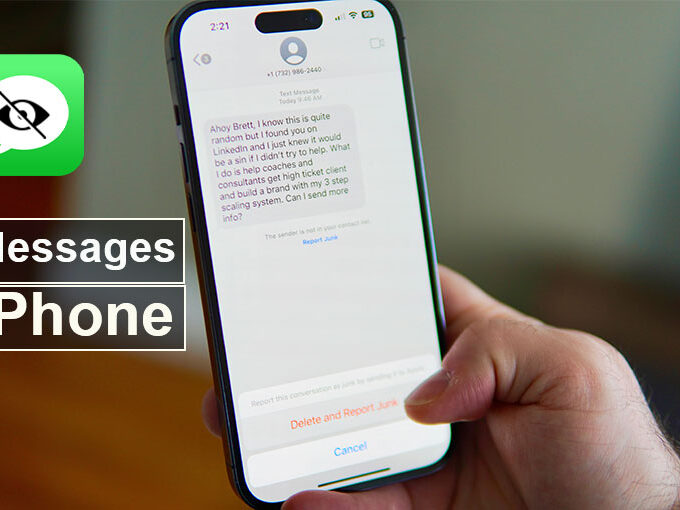
2. Phishing attacks
Phishing attacks could impact any software program. An attacker will attempt to trick you into providing your password or any other sensitive information through phishing attacks. They may pretend to be a legitimate website, program, or website. You should be cautious about emails and messages asking for personal information. Never click on any links in such messages unless you are certain they are legitimate.
Phishing can happen via software programs as well as messaging programs like Skype and Facebook Messenger or email programs like Gmail. You should be careful about attachments and links you receive from these programs.
3. Keyloggers
Keyloggers are malicious programs that can be installed on your computer without you knowing. They can track your keystrokes, making it possible to steal passwords or other sensitive information. Keyloggers can also be downloaded via email attachments, malicious websites, or infected USB drives.
Never install untrustworthy software to protect yourself against keyloggers. You should be very cautious about which emails you open and which websites you visit. To remove a keylogger from your computer, you should run a malware scanner as soon as possible.
4. Drive-by Downloads
Drive-by downloading is another type of malicious software you can install on your computer without your permission. These programs can be downloaded when you visit malicious websites or click on malicious links. They can track your browsing habits and steal passwords once they are installed.
Drive-by downloads can be prevented by being careful about which websites you visit and the links you click. Run a malware scan immediately if you suspect you have downloaded a dangerous program.
5. Malware
Malware is malicious software that infects your computer without your knowledge. Once it’s installed, it can steal your passwords and data, or allow remote access by an attacker to your computer. An attacker could gain access to your IT infrastructure. Take care of what attachments you open in email and which websites you visit. These are the two most common ways that malware can get onto your computer.
You can also use the software to insert ransomware into your system. An attacker could fake a popular program and then distribute it online. Users unknowingly give the attacker access to their systems by downloading and installing the fake software. An attacker could also exploit software vulnerabilities to gain access to the user’s system. Once inside, the attacker can install ransomware on the victim’s computer and encrypt their files.
6. Unsecured Wi-Fi Networks
You could be at risk if you connect to public Wi-Fi networks in order to access the internet. Networks are often unsecured, meaning that any other person on the network could see your traffic and monitor it. Use public Wi-Fi only if you have a secure VPN. This will ensure that your traffic is private and encrypted.
7. Social Engineering
Social engineering is a form of attack in which an attacker attempts to trick you into giving them access to your account and data. They may pose as customer support agents for programs you use and ask for your password to “fix” any issues in your account.
You may receive an email from them that appears to be from a trusted source, but contains malicious links. Even if the communication appears to be legitimate, you should be very cautious about what you receive.
8. Unsafe Browser Extensions
Use a web browser such as Mozilla Firefox or Google Chrome to access you may have installed extensions to enhance functionality or features. However, some extensions could pose security risks. An extension may have access to your web browser and any data you input. Be very selective about which extensions you install, and only install ones from trusted sources.
Also read: 15 Best Google Chrome Security Extensions You Should Use
9. WordPress Plugins
Be careful when installing plugins to your WordPress website. Some plugins could pose security risks by allowing attackers to access your website or database. Only install trusted plugins and ensure that they are kept up to date. It is also important to ensure that plugins are being downloaded and installed regularly while you browse new plugins. Before you decide to install the software, take a look at when it was last updated.
10. Adware
Adware is software that displays advertisements on your computer. Often, it appears as pop-up ads. Although not all adware can be malicious, it can track your online activities as well as collect sensitive information such as passwords and credit card numbers. Always be careful with the programs you install and make sure to read the EULA before you agree to anything.
11. Google Docs
Google Docs is a cloud-based word processor application that is part of Google Workspace. Although it is generally safe, some malicious actors have used it to launch phishing attacks or spread malware. Google Docs is safe to use, but you should only trust the documents you open and not click on any links within them.
12. Third-Party App Stores
You may find it tempting to download apps from third-party stores instead of the official Google Play Store if you have an Android phone. Although there are legitimate app stores, many are full of malware or other malicious programs. To avoid these risks, it’s best to use the official app store on your device.
13. Outdated software
The most important thing. What you can do to keep your computer safe is to make sure all of your software is updated to the latest version. Software developers release regular updates to fix security vulnerabilities. It’s crucial to update as soon as possible. Your software can usually be set to update you can either check for updates automatically or manually.
Also read: Top 10 Bug Tracking Tools and Software
14. Commandeering For Loops
Commandeering for loops refers to a method of attacking your computer where the attacker sends malicious commands through the command-line interface. This could happen if you accidentally install and run malicious programs or if your computer is compromised by hackers. This type of attack can be prevented by being careful about what programs you download or run, and only visiting websites you trust.
15. Lack of Security Features
Many popular software programs lack basic security features or lose functionality. This leaves users at risk of being attacked. Adobe Reader and Microsoft Word, for example, have been shown to be vulnerable to security attacks. These programs should be kept up-to-date with security patches.
Are you worried about downtime when installing software updates? You can schedule them for a time you don’t plan to use your computer. You can rest assured that your software is up-to-date, secure, and always available.
Conclusion
Software in all its many forms is essential for both running our businesses and improving our personal lives. It is nearly impossible to not use dozens of programs every day. Even the most basic of software can be a security risk if not properly used. Understanding the attack vectors in advance can help you and your company protect your data.









Leave a comment